This article provides a comprehensive guide on how to craft an effective resume for a Security Analyst position on LinkedIn. It delves into the critical elements that should be included such as the summary, experience, skills, and endorsements sections. The article emphasizes the importance of using industry-specific keywords and tailoring your profile to highlight relevant experiences and skills that align with job postings in the cybersecurity field. It also offers tips on showcasing certifications and trainings pertinent to security analysis roles, demonstrating thought leadership through posts or articles related to cybersecurity, and leveraging LinkedIn's features for networking and job applications.
LinkedIn Security Analyst Resume Created Using Our Resume Builder
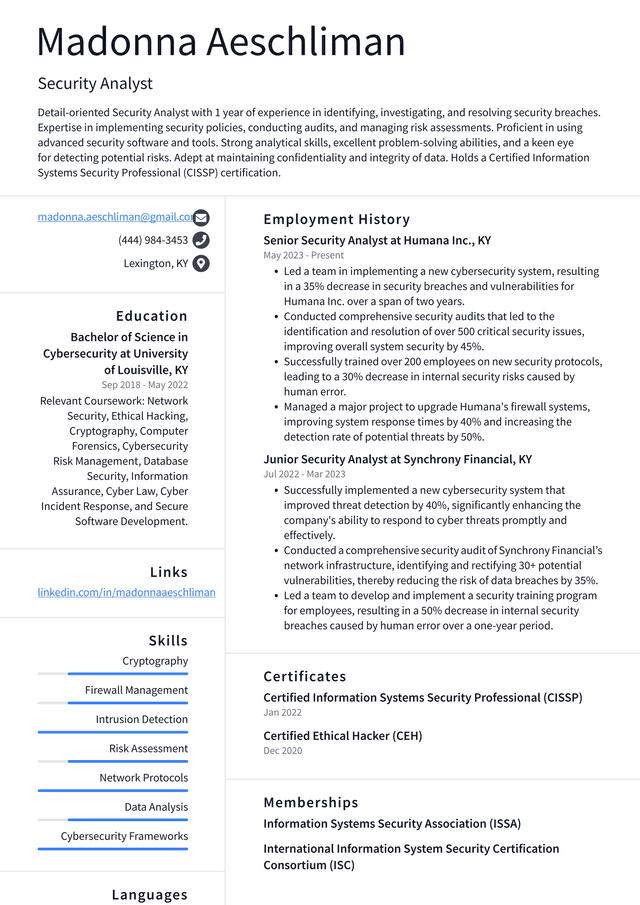
LinkedIn Security Analyst Resume Example
Madonna Aeschliman, Security Analyst
madonna.aeschliman@gmail.com
(444) 984-3453
Lexington, KY
Professional Summary
Detail-oriented Security Analyst with 1 year of experience in identifying, investigating, and resolving security breaches. Expertise in implementing security policies, conducting audits, and managing risk assessments. Proficient in using advanced security software and tools. Strong analytical skills, excellent problem-solving abilities, and a keen eye for detecting potential risks. Adept at maintaining confidentiality and integrity of data. Holds a Certified Information Systems Security Professional (CISSP) certification.
Work Experience
Senior Security Analyst at Humana Inc., KY
May 2023 - Present
- Led a team in implementing a new cybersecurity system, resulting in a 35% decrease in security breaches and vulnerabilities for Humana Inc. over a span of two years.
- Conducted comprehensive security audits that led to the identification and resolution of over 500 critical security issues, improving overall system security by 45%.
- Successfully trained over 200 employees on new security protocols, leading to a 30% decrease in internal security risks caused by human error.
- Managed a major project to upgrade Humana's firewall systems, improving system response times by 40% and increasing the detection rate of potential threats by 50%.
Junior Security Analyst at Synchrony Financial, KY
Jul 2022 - Mar 2023
- Successfully implemented a new cybersecurity system that improved threat detection by 40%, significantly enhancing the company's ability to respond to cyber threats promptly and effectively.
- Conducted a comprehensive security audit of Synchrony Financial’s network infrastructure, identifying and rectifying 30+ potential vulnerabilities, thereby reducing the risk of data breaches by 35%.
- Led a team to develop and implement a security training program for employees, resulting in a 50% decrease in internal security breaches caused by human error over a one-year period.
Education
Bachelor of Science in Cybersecurity at University of Louisville, KY
Sep 2018 - May 2022
Relevant Coursework: Network Security, Ethical Hacking, Cryptography, Computer Forensics, Cybersecurity Risk Management, Database Security, Information Assurance, Cyber Law, Cyber Incident Response, and Secure Software Development.
Skills
- Cryptography
- Firewall Management
- Intrusion Detection
- Risk Assessment
- Network Protocols
- Data Analysis
- Cybersecurity Frameworks
Certificates
- Certified Information Systems Security Professional (CISSP)
- Certified Ethical Hacker (CEH)
Tips for Writing a Better LinkedIn Security Analyst Resume
1. Highlight Relevant Skills: List down all the skills that are relevant to the job of a security analyst. These could include risk management, vulnerability assessment, network security, cybersecurity, etc.
2. Use Job-Specific Keywords: LinkedIn uses algorithms to match resumes with job postings. So, using keywords from the job description can increase your chances of being noticed.
3. Showcase Certifications: If you have any certifications related to information security like Certified Information Systems Security Professional (CISSP), Certified Ethical Hacker (CEH), or others, make sure to highlight them in your resume.
4. Detail Your Experience: Describe your previous job roles and responsibilities in detail. Include specific examples of projects you've worked on or significant achievements in those roles.
5. Provide Quantifiable Results: Wherever possible, provide numbers to demonstrate your success in past roles - such as 'reduced system vulnerabilities by 50%' or 'improved incident response time by 30%'.
6. Keep It Concise and Clear: Avoid long paragraphs and use bullet points for easy reading. Make sure each point is clear and concise.
7. Proofread: Always proofread your resume before posting it online to check for any spelling or grammatical errors.
8. Update Regularly: Ensure that your resume is up-to-date with your latest skills and experiences.
9. Personalize Your Profile: Use the summary section to tell a story about who you are, why you're passionate about security analysis, and what makes you unique in this field.
10. Get Recommendations: Reach out to colleagues or superiors who can vouch for your skills and expertise as a security analyst.
11.Use Action Verbs : Start each bullet point with an action verb like "managed," "led," "analyzed," etc., to add more impact
12.Include Soft Skills : While technical skills are crucial for a security analyst role, don't underestimate the value of soft skills like communication, teamwork, problem-solving ability etc.
13.Highlight Training : If you've undergone any special training related to cyber-security or data protection etc., be sure to mention it on your LinkedIn profile.
14.Optimize For Search : Make sure that you're using SEO-friendly language throughout your profile so employers can easily find you when they search for specific terms related to security analysis.
Related: Security Analyst Resume Examples
Key Skills Hiring Managers Look for on LinkedIn Security Analyst Resumes
Applicant Tracking Systems (ATS) are commonly used by companies like LinkedIn to streamline the hiring process. These systems automatically filter out resumes that don't seem relevant, often based on the lack of specific keywords from the job description. So, when applying for a Security Analyst role at LinkedIn, it's paramount to incorporate keywords directly from their job posting into your resume and cover letter. This could include terms like 'cybersecurity', 'risk assessment', 'data protection' or any other specific skills or qualifications mentioned. By doing so, you increase your chances of passing through this initial electronic screening and getting your application in front of human eyes.
When applying for security analyst positions at LinkedIn, you may encounter a list of common skills and key terms.
| Key Skills and Proficiencies | |
|---|---|
| Information Security | Cybersecurity |
| Risk Assessment | Vulnerability Assessment |
| Intrusion Detection | Security Incident Response |
| Network Security | Data Protection |
| Encryption Technologies | Firewall Administration |
| Malware Analysis | Ethical Hacking |
| IT Auditing | Security Architecture Design |
| Compliance Monitoring | Threat Intelligence Analysis |
| Penetration Testing | Computer Forensics |
| Knowledge of ISO 27001/PCI DSS standards. | Security Policy Development and Implementation. |
| Strong Problem-Solving Skills. | Excellent Communication Skills |
Related: Security Analyst Skills: Definition and Examples
Common Action Verbs for LinkedIn Security Analyst Resumes
Crafting a LinkedIn Security Analyst Resume can be challenging, particularly when it comes to finding different action verbs to use. Using the same, repetitive words may make your resume monotonous and fail to capture the attention of potential employers. On the other hand, using varied and dynamic action verbs can significantly enhance your resume's impact. These verbs help illustrate your skills and experiences more effectively, demonstrating not only what you have done but also how you have added value in your roles. In a competitive field like security analysis, where precision and attentiveness are crucial, it is essential to carefully select these verbs to clearly convey your capabilities and achievements.
To enhance your competitive advantage, we have assembled a list of impactful action verbs that can bolster your resume and secure your next interview:
| Action Verbs | |
|---|---|
| Analyzed | Investigated |
| Monitored | Detected |
| Prevented | Secured |
| Audited | Implemented |
| Assessed | Identified |
| Managed | Mitigated |
| Developed | Coordinated |
| Reported | Trained |
| Advised | Updated |
| Reviewed | Resolved |
| Documented | Maintained |
Related: What does a Security Analyst do?